Blog article
- 8 minutes read

- Waseem Osman
- DMARC Practitioner
DANE Authentication: What Enterprise Security Leaders Need to Know
DANE authentication overview:
- DANE prevents attackers from using fraudulent certificates to intercept email traffic
- DANE secures the transport layer, complementing DMARC rather than replacing it
- DANE requires DNSSEC – without it, the protocol can’t function securely
- DANE’s operational burden comes from key rotation, not certificate renewal
- DANE failures are silent by default – TLS-RPT monitoring is essential
DNS-based Authentication of Named Entities (DANE) is one of the most underutilized protocols in enterprise email security.
Most organizations focus on sender verification and overlook transport-layer security entirely. This leaves a significant vulnerability: The potential for Man-in-the-Middle (MitM) attacks that can intercept email communications even when sender authentication passes.
What DANE Does in Your Email Security Stack
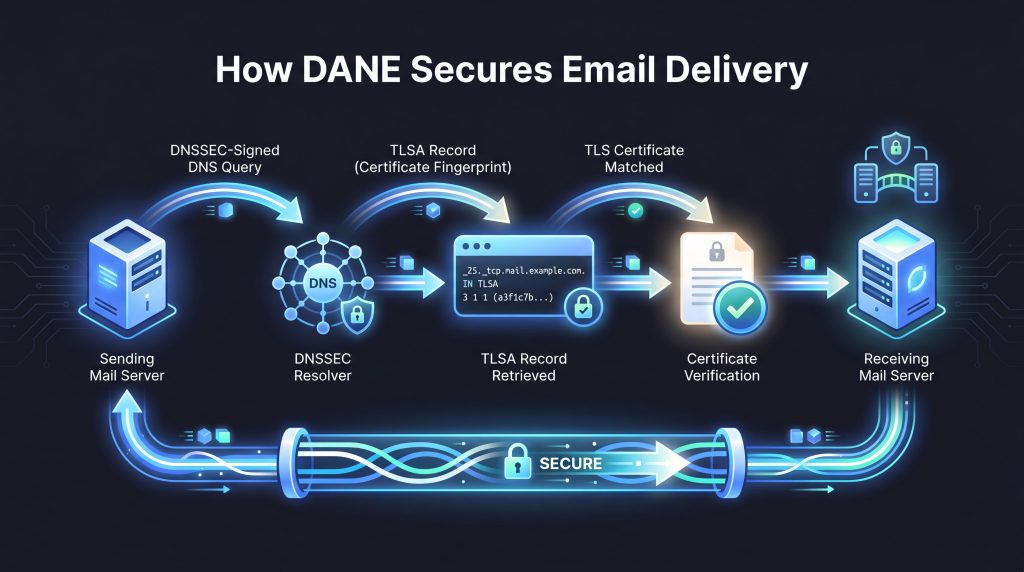
DANE allows domain owners to publish TLSA records in their DNS that specify which TLS certificates are authorized for a particular service. When implemented correctly, DANE prevents attackers from using fraudulent certificates to intercept email traffic between servers – even if they’ve compromised a Certificate Authority (CA) or obtained a valid certificate through social engineering.
Unlike DMARC, which focuses on message authentication, DANE secures the transport layer. This makes it a complementary technology rather than a competing one. Your DMARC policy might successfully authenticate a sender, but without DANE, that authenticated message could still be intercepted and read during transmission.
DMARC tells receiving servers whether a message is legitimate based on sender authentication. DANE tells receiving servers whether the TLS connection itself is legitimate based on certificate authentication. Both address different attack vectors.
Why DANE Deployment Remains Low
The technical specifications for DANE are well established, but enterprises face several operational hurdles, which can help explain its low adoption rate.
DNSSEC prerequisites are the most significant barrier. DANE requires DNSSEC validation to function securely, which means businesses must first implement and maintain it for their email domains.
Many enterprises still lack comprehensive DNSSEC coverage, treating it as an additional operational burden rather than a foundational security control. Without a fully signed DNS zone and a complete chain of trust, TLSA records are ignored by compliant sending servers.
Certificate management is the second major consideration, though it’s more nuanced than it first appears.
The recommended DANE configuration for SMTP is DANE-EE with SPKI and SHA-256, written as 3 1 1. Specified in RFC 7671 and RFC 7672, this configuration pins the public key fingerprint rather than the full certificate. If you renew your certificate using the same key pair, your TLSA record doesn’t need to change.
The operational burden arises when you change the key pair. When a company rotates to a new key pair, a roll-over period is required: The new TLSA record must be published and given time to propagate before the old certificate is retired. Getting this timing wrong can cause legitimate emails to be rejected.
Making the Decision to Deploy DANE
DANE deployment isn’t right for every organization. The decision should be based on risk, operational readiness, and infrastructure.
Risk is the first consideration. Enterprises handling sensitive communications or operating in regulated industries are more likely to find that DANE’s transport security benefits justify the operational overhead. CA compromise is a real threat, and DANE addresses it directly.
Operational readiness is equally important. DANE implementation requires mature DNS operations, DNSSEC coverage, and key lifecycle management processes. Businesses lacking these capabilities should address those foundational gaps before attempting deployment.
Infrastructure is the final consideration. Check whether cloud email providers manage DANE on your behalf, whether security gateways can handle DANE validation, and whether monitoring systems provide adequate visibility into DANE-specific failure modes through TLS-RPT.
Monitoring DANE in Production
DANE failures are silent by default. When a sending server can’t validate your TLSA record, it defers or rejects delivery without necessarily notifying you. TLS-RPT (RFC 8460) provides the visibility needed to catch this.
TLS-RPT reports include DANE-specific failure types – most commonly dane-policy-failure, which occurs when a certificate renewal changes key material without a corresponding TLSA update. These reports surface DANE failures before your sending partners start reporting delivery problems.
How DANE Fits with Existing Email Infrastructure
DANE implementation must account for every component in your environment – email servers, security gateways, cloud providers, and third-party services – not just your primary sending infrastructure.
Cloud providers present particular considerations. Major providers like Microsoft Exchange Online have implemented DANE for their own infrastructure, meaning companies using those services benefit from DANE on inbound email, and TLSA record management is handled on their behalf.
Security gateway integration requires careful planning. Enterprises relying on secure email gateways for malware scanning and content filtering need those gateways to be DANE-aware to avoid breaking the certificate validation chain. Legacy gateways may require updates or replacement to support DANE properly.
How Sendmarc Can Help
Sendmarc’s TLS-RPT management gives teams direct visibility into transport-layer failures, including DANE-specific errors like dane-policy-failure, before they affect deliverability.